The XZ Utils Backdoor: How "Jia Tan" Infiltrated Linux


The Multi-Year Grooming of the Open-Source Supply Chain
The infiltration of XZ Utils (CVE-2024-3094) was not a quick hack but a patient, multi-year social engineering campaign. Starting around 2021, an entity using the pseudonym Jia Tan began contributing small, legitimate patches to the XZ project.
The attacker leveraged sockpuppet accounts—fake identities like "Jigar Kumar"—to harass the original maintainer, Lasse Collin. These accounts pressured Lasse Collin to hand over control, citing his slow response times due to mental health struggles. By 2023, Jia Tan had successfully gained "Co-Maintainer" status, granting them the authority to commit code directly to the repository and manage the release of new versions.
Weaponizing the Build Process via Binary Blobs
The technical brilliance of the backdoor lay in its obfuscation. Instead of placing malicious C code directly into the source files—where it might be caught by "the many eyes" of the open-source community—the attacker hid the payload inside "binary blobs." These are large, non-human-readable files typically used for testing compression algorithms.
 A humorous comic strip about an anonymous individual supporting the entire digital infrastructure as we know it - Photo: xkcd/Randall Munroe
A humorous comic strip about an anonymous individual supporting the entire digital infrastructure as we know it - Photo: xkcd/Randall Munroe
During the compilation process, a series of complex, hidden scripts in the m4 macro directory would extract the payload from these test files. The backdoor was specifically designed to target OpenSSH by intercepting the RSA public key decryption process. If a specific private key (held by the attacker) was used during an SSH login attempt, the backdoor would bypass authentication and grant the attacker root access to the server.
The "Goldilocks Zone" of Dynamic Linking
What competitors and standard news reports often skip is the precision required to hit the "Goldilock Zone" of the Linux Global Offset Table (GOT). The backdoor utilized a mechanism called an IFUNC (Indirect Function) resolver. This is a legitimate feature used to select the most efficient version of a function based on the user's hardware (e.g., Intel vs. AMD).
The attacker manipulated this resolver to run malicious code extremely early in the program's execution. By doing so, they could overwrite the memory address of the RSA_public_decrypt function before the system marked that memory as "read-only." This narrow window of time—after the function is mapped but before it is locked—is the only moment such a deep system hijack can occur without crashing the server.
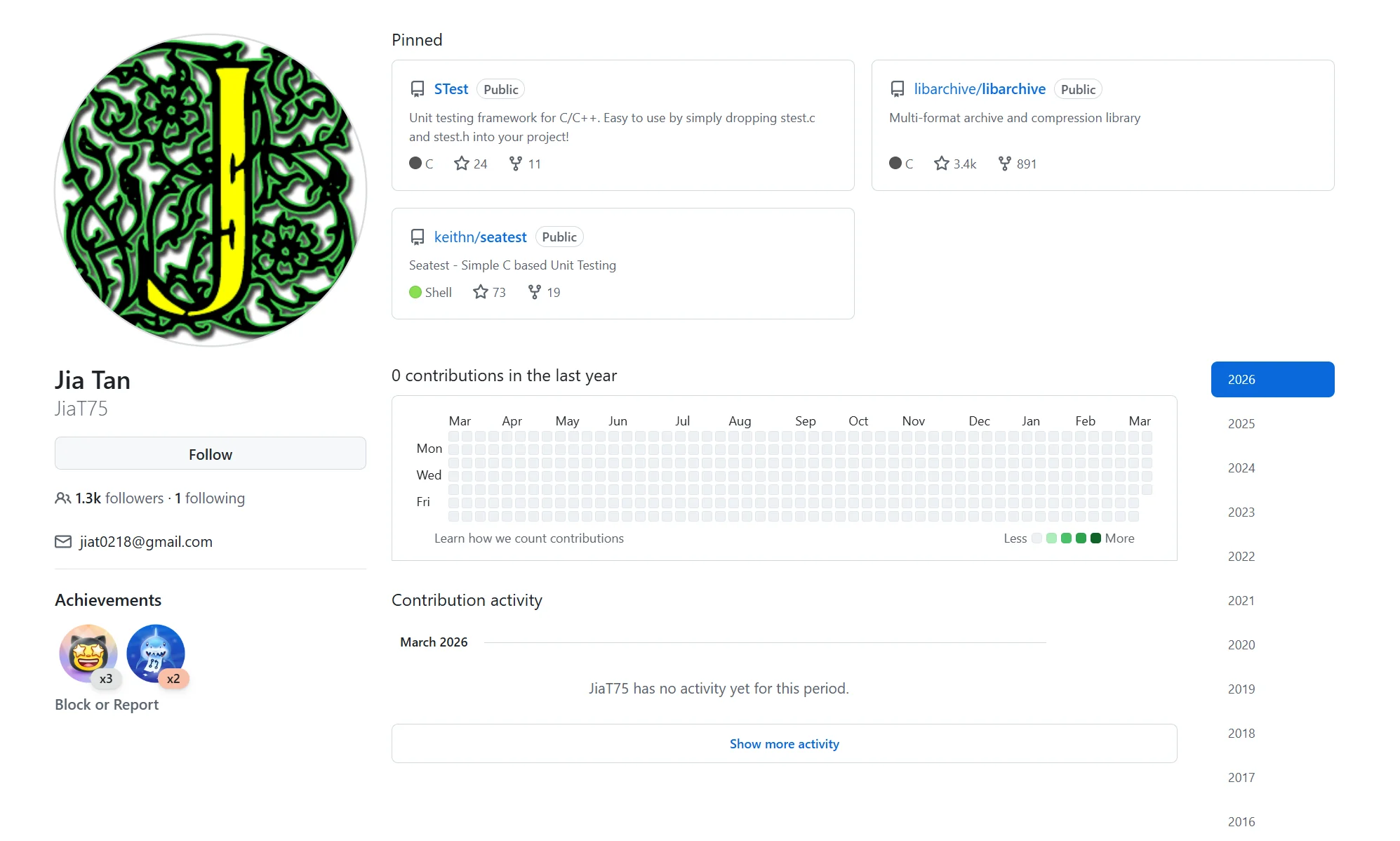 Jia Tan's Github page (The XZ Utils Infiltration: A Masterclass in Long-Game Cyber Espionage)
Jia Tan's Github page (The XZ Utils Infiltration: A Masterclass in Long-Game Cyber Espionage)
Timeline of the XZ Utils Infiltration
| Date | Key Event | Entity Involved |
|---|---|---|
| 2021-10-29 | First contribution from "Jia Tan" to XZ Utils | Jia Tan |
| 2022-05-19 | Sockpuppet accounts begin pressuring the maintainer | Lasse Collin |
| 2023-01-07 | Jia Tan gains commit access to the repository | GitHub |
| 2024-02-24 | Malicious version 5.6.0 is released | Debian / Fedora |
| 2024-03-29 | Backdoor discovered due to a 500ms latency lag | Andres Freund |
Systemic Fragility of the Maintainer Ecosystem
This incident highlights a structural shift in how we perceive the security of the Linux ecosystem. The "Linus’s Law"—that with enough eyeballs, all bugs are shallow—failed here because the eyeballs were looking at the source code, while the bug was hidden in the build environment and binary data.
The cybersecurity sector now recognizes that the most critical infrastructure on the planet often rests on the shoulders of single, unpaid volunteers. This "Human Dependency" is a systemic risk that nation-state actors, potentially groups like APT29 (Cozy Bear), are now actively exploiting. The focus of security is shifting from "vulnerability scanning" to "provenance verification," ensuring that every line of code can be traced to a verified human identity.
The Future of Cryptographic Supply Chain Integrity
The discovery of the XZ backdoor by Andres Freund, a Microsoft engineer who noticed a mere 500-millisecond delay in SSH login times, was a stroke of incredible luck. Had the attacker optimized the code to be 20% faster, the backdoor might have migrated into Red Hat Enterprise Linux and stabilized for years.
The fallout is forcing a regulatory and technical pivot toward "Reproducible Builds" and mandatory Software Bill of Materials (SBOM) for critical utilities. However, as long as the global economy relies on open-source libraries maintained by burnt-out volunteers, the window remains open for the next sophisticated actor to play the long game.
References:

Comments (1)
Please login to comment
Sign in to share your thoughts and connect with the community
Loading...